As a proud alumnus of the Marine Corps (OMB Breach), filer of SEC materials (SEC breach), and card-carrying member of credit card carrying people (Equifax breach), not a week goes by without some headline reminding me that my entire financial history is probably stored on some foreign government’s server (along with millions of other Americans).
Long story short, I am fairly confident that my personal information is on a Russian billboard somewhere.
Against this backdrop of titanic security breaches, the SEC is gearing up a new inspections group focused exclusively on cyber, and I would be shocked if cybersecurity is not the top priority in their Examination Priorities letter to be released in early January.
But don’t worry, this is not another article discussing how important cybersecurity is–it is important–we all know this fact. Rather, this post will try to help financial advisors understand how they can actually get started building a respectable cybersecurity program.
Four Simple Steps to Get An Advisor Cybersecurity Policy Up and Running
I meet countless Advisors that have yet to enact a robust cybersecurity program, let alone know where to start. Conversely, I speak with other Advisors that are paying top dollar (or more specifically, tens of thousands of dollars) for common sense solutions that can be done easily with a little bit of research. There appears to be no happy medium. You are either relatively unprepared (not good) or paying through the nose without really understanding what to do (not good either).
In the spirit of empowering (investors) through education, we figured we would share our best practices and lessons learned in cybersecurity. If you are a client of an advisor, you can use this guide to help ask your advisor the right questions…If you are an advisor, we hope this article will give you some basic building blocks to get a robust cyber program off the ground (free!). And of course, please send us your thoughts and feedback so that we can learn with you — we don’t claim to have a monopoly on good ideas!
So how does a financial advisor build a cybersecurity program? There are four simple, but not easy, steps to follow:
- Get the rulebook
- Write the manual
- Implement the manual
- Assess and Improve
I would recommend doing steps 1-4, to the best of your availability, BEFORE you start paying third parties. Come to a third party for review after you have drafted what you think is best in class. This process will ensure you can ask smart questions, enable you to push back on high fees, and most importantly, you will learn how and why to implement a particular process.
Remember, while the SEC cares about the policies you have in place, they really want to see HOW you actually implement your stated policies.
Step One: Get the Cybersecurity Rulebook
The de facto starting point for any Cyber compliance program is the National Institute of Standards and Technology (NIST) Cybersecurity Framework. NIST is a federally sponsored organization that basically hires the best and brightest cyber minds on the planet, as well as engages leading intellectuals on cybersecurity across the country. Every couple of years, they release a newly updated Cybersecurity Framework. This document outlines what businesses of all types need to do in order to maintain a great cyber program.

Note: Author will neither confirm nor deny that he may be the second from the right in the blue shirt.
NIST doesn’t mess around. They publish cyber guidelines on virtually everything:
- Need a whitepaper on how to write your Business Continuity Plan (BCP) for a malware attack?
- How about training standards for cybersecurity awareness?
- What if you just want to learn more about the fundamentals of cybersecurity for a small business?
If you need the expert guidance, chances are that NIST can give you the best practices you seek…in spades.
But the NIST framework, while terrific, is a general rulebook that is not custom tailored to advisors. It doesn’t outline specifically what, advisors need to do, when, and how. For this level of specificity, I would download the following:
- FINRA’s small firm cybersecurity checklist
- SEC’s Office of Compliance, Inspections, and Examinations cybersecurity press releases (2015 is my favorite)
Let’s start with FINRA. FINRA has basically taken the NIST standards and updated it to reflect the nuance of a small advisory firm. Also, you can use this checklist annually as part of a risk assessment tool to augment and enhance your program. Risk assessments are an annual requirement for cyber programs anyway, so now you are covered!
Next, turn to the SEC and review the 2015 report (link above) and scroll to the appendix. The SEC has basically given you the (probable) exam questions, in advance, for a routine cybersecurity audit. Granted, the memo is a few years old and nothing is going to be all-inclusive; however, if you are meeting the standards outlined in the exam memo, you will be better prepared for an audit.
So there you go. You now have, for free, the best and brightest minds in cybersecurity (1) laying out the framework, (2) the enabling oversight agency (FINRA) building a straightforward tool for you to use, and (3) the referees of the industry (SEC) providing the probable questions. Plus, you have a template manual to review and get started with. Read these manuals and get your feet wet BEFORE you contract a high-cost compliance consultant to help you. You will ask better questions and they will provide a more value-added service.
Step Two: Writing the Cybersecurity Manual
Notice that the heading of this section isn’t “copying” the manual or “buying” the manual. I can not stress how much value you will derive from writing your own compliance manual. Why? The first day of your SEC exam, you will be met with a team of anywhere from 3-5 regulators. All of them will be very nice and very professional. They will also have a highly accurate BS meter — these teams perform numerous exams a year and have seen it all. As you start answering SEC questions about your cybersecurity program, it will become very apparent, very quickly, as to what you know and what you don’t.
For example, if you can’t tell the difference between a Pen Test and a DDOS monitoring service, encryption at rest and encryption in transit, and explain your company’s view on thumb drives in the office, it will be clear as to how much (or little) you know about cyber. Writing the manual forces the mind to learn the concepts. At the end of the day, this is not about passing an exam, it’s about protecting your clients and ensuring your viability as a business. It’s more painful in the short term than taking the easy road, but you will reap tremendous dividends down the road.
Drafting the first advisor cybersecurity manual (Philadelphia, circa 1978)
This does not have to be pretty. Copy the formatting from your compliance manual and use the same sections outlined in NIST. Write a draft, reference the SEC examination memo above, and then refine further with the small firm cybersecurity checklist.
Now you have a fundamental understanding of the requirements. You are also 10x better equipped to quiz potential service providers. In addition, it is a lot cheaper to send this manual to Counsel and ask for a final review as opposed to hiring a lawyer or cyber consultant to write your program from scratch.
Step Three: Implement the Manual
A cybersecurity program is not a pdf file that you downloaded online. Similarly, a cybersecurity program is not a signed contract with a third party that does everything for you. You must always remember: the only person that gives a flip about your cybersecurity program is you. If a breach occurs, your clients will be calling you, not your contractor. When exam time comes, it is you and the SEC. Of course, you can (and should) delegate for efficiency’s sake, but you can never delegate accountability. Whoever is responsible for your cyber program, I would task that individual with “extreme ownership“.
What does “implement the manual” actually mean? Some Advisors we speak with have the following experience during exam time:
SEC: Hi, thanks for having us. To get started, do you mind sharing your compliance manual?
Advisor: Sure! Here you go! (Advisor hands over dusty, yellowed compliance manual they printed from their “compliance provider”, last update: 2002)
SEC: Thanks…uhm…can you go ahead and show us how you do all of this?
Advisor: Huh?
SEC: You know, like how you do all of the stuff in your Cyber Manual? For example, it says that you inventory all of your hardware. Can you show us your hardware inventory?
Advisor: (Knees shaking) Uhm…yes….uhm, would you all be interested in some coffee???

Note1: The image above is not a real SEC examinerNote2: SEC examiners are actually really nice people just trying to do their jobsNote3: The author apologizes for portraying examiners in this light for a cheap laughNote 4: If you don’t have a good cyber program after reading this post, you deserve to have the Incredible Hulk as your SEC examiner anyway
The Manual is the easy part. Implementation is the hard part. You will most certainly need some form of reminder system to help you stay on top of the tasks and action items described in your manual. Not surprisingly, there is no shortage of service providers that will give you some form of compliance monitoring/support/implementation (and take your money). I will outline two options for you to consider that are low cost and common sense:
Option 1: Good ol’ fashioned Excel
Yes, my friends. Excel. You can build a best in class compliance system with Excel. Why? Compliance is nothing more than a bunch of processes. You list processes, put due dates by processes, and then check the list to ensure the processes are complete. Remember, it’s not the actual tool or manual that makes the program, it’s the user making sure it gets done. If Excel is the only program you are comfortable with, then go for it. Here are your column headings:
Column 1: Warning Date (When should you start thinking about this?)
Column 2: Due Date (When must this compliance task be complete?)
Column 3: Task (What do you need to do?)
Column 4: Task Description (How do you do it?)
Column 5: Relevant NIST Framework Best Practice (See Table 2 in the NIST Cybersecurity Framework)
If you have a regularly updated, implemented cybersecurity spreadsheet in Excel that references the most current NIST framework, you are likely leaps and bounds ahead of your peers, as well as you have the internal know how to implement effectively. Cost? Zero.
Option 2: SmartSheet
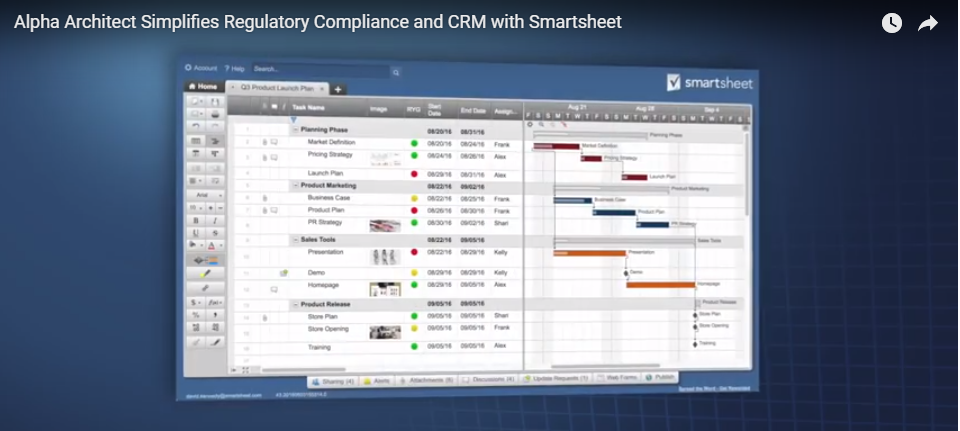
Smartsheet…it rocks
Smartsheet is basically Excel and MS Project combined, but integrated into your email and then pumped up with a ton of cool features. For a guy like me that can barely set the clock on his microwave, the software is super user-friendly and easy to learn. I learned the basics in a few hours. We use this tool for everything and it has created a distinct competitive advantage for us. Affordable Alpha isn’t just a tagline for our firm…we actually have to implement systems that enable us to become radically more efficient.
Here’s a video on the subject:
Note: we use SmartSheet for all task management and workflow requirements: Compliance, Cyber, Trading Calendar, CRM, you name it. Over several years, we found that building our own custom processes was cheaper and more effective than cobbling together a myriad of service provider tools. One platform. One price-tag. Cost? $15 per user, per month. No – we don’t get paid by Smartsheet to write this stuff and no, we aren’t getting free services for pumping their software. It’s just darn good software at a great price.
You basically follow the same framework as the Excel option but you can add automated email reminders, build a custom dashboard (red/yellow/green) enable automated approval requests, etc. (We have this integrated with Google G-Suite). Most importantly, every action is time stamped, backed up, and documented so you don’t need to worry about who is doing what/when. If you want to dive into the details here, drop me a note and we can chat through the basics.
Step 4: Assess and Improve
The most important step. Cybersecurity threats are changing, as are the tools by which to combat them. If you notice, the Cybersecurity Framework I mention above is in redline draft form. It is being updated as we speak. Your cybersecurity manual should be the same. At our firm, we do a quarterly review of existing cyber practices, with an annual risk assessment and overhaul every year. We time the review to take place in the summer when things are a bit slower and the office is a bit quieter.
Conclusion: You can DIY Advisor Cybersecurity
Advisors can (and should) take the reins on cybersecurity. The benefits are tremendous. Stronger defenses, lower costs, and most importantly, a meaningful program is established that actually places ownership where it matters most. Getting started is relatively straightforward and does not require significant upfront costs. The frameworks and manuals for Advisors are readily available, and simple tools can empower any advisory to implement (and document) their cyber program.
Granted, cybersecurity requires investments. We engage a myriad of service providers in the construction and maintenance of a holistic, defense-in-depth cybersecurtity program. In addition, we retain counsel to ensure we are current with existing regulations. We are not advocating for DIY dentistry here, but rather, we hope the framework shared today provides a foundation of knowledge and ownership for advisors.
Finally, we are all in this together. Sharing lessons learned, highlighting cool tools that help lower costs, etc. are in everyone’s best interest. Hit with questions and be expected for me to reciprocate!
Disclaimer: OK…so here are a few points to remember as you read this. This is free advice/lessons learned. Always consult with an expert, lawyer, whatever as you formalize a program. Also, there are a million ways to improve cybersecurity and all of the tools/links/tidbits above will surely be missing something. Please consider this post a starting point in what is a long-term, continuous effort.
About the Author: Pat Cleary
—
Important Disclosures
For informational and educational purposes only and should not be construed as specific investment, accounting, legal, or tax advice. Certain information is deemed to be reliable, but its accuracy and completeness cannot be guaranteed. Third party information may become outdated or otherwise superseded without notice. Neither the Securities and Exchange Commission (SEC) nor any other federal or state agency has approved, determined the accuracy, or confirmed the adequacy of this article.
The views and opinions expressed herein are those of the author and do not necessarily reflect the views of Alpha Architect, its affiliates or its employees. Our full disclosures are available here. Definitions of common statistics used in our analysis are available here (towards the bottom).
Join thousands of other readers and subscribe to our blog.